It is interesting to note that the riskiness of operational spreadsheets are overlooked even by companies with high standards of risk management. Only when errors amount to actual losses do they realize that these risks have been staring them in the face all along.
Common spreadsheet risk issues
Susceptibility to trivial manual errors
Due to the fundamental structure of spreadsheets, a slight change in the formula or value in any of their inhabited cells may already affect their overall output. An
- accidental copy-paste,
- omission of a negative sign,
- erroneous range selection,
- incorrect data input or
- unintentional deletion of a character,cell, range, column, or row
are just some of the simple errors spreadsheet users frequently encounter. Rarely are there any counter-checking controls in place in a spreadsheet-based activity and manual errors therefore easily go undetected.
Possibility of the user working on the wrong version
How do you store spreadsheet files?
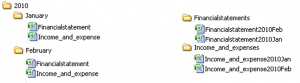
Since the most common reports are usually generated on a monthly basis, users tend to store them using variations of these two configurations:
If you notice, a user can accidentally work on the wrong version with any of these structures.
Prone to inconsistent company-wide reporting
This happens when a summary or ?final? spreadsheet is fed information by different departments coming from their own spreadsheets. Even if most of the data in their spreadsheets come from one source (the company-wide database), erroneous copy-pasting and linking, or even different interpretations of the same data can result to contradicting information in the end.
Often defenceless against unauthorised access
Some spreadsheets contain information needed by various individuals or department units in an organisation. Hence, they are often shared via email or through shared folders in a network. Now, because spreadsheets don’t normally use any access control, any user can easily open a spreadsheet file and view or modify the contents as he wishes.
Highly vulnerable to fraud
A complex spreadsheet system with zero or very minimal controls provides the perfect setting for would-be fraudsters. Hidden cells with malicious formulas and links to bogus information can go unnoticed for a long time especially if the final figures don’t deviate much from expected values.
Spreadsheet risk mitigation solutions may not suffice
Inherent complexity makes testing and logic inspection very time consuming
Deep testing can uncover possible errors hidden in spreadsheet cells and consequently mitigate risks. But spreadsheets used to support financial reporting are normally large, complex, highly-personalised and, without ample supporting documentation, understandably hard to follow.
No clear ownership of risk management responsibilities
There?s always a dilemma when an organisation starts assigning risk management responsibilities for spreadsheets. IT personnel believe users in the business side of the organisation should be responsible since they are the ones who create, edit, store, duplicate, and share the spreadsheet files. On the other hand, users believe IT should be responsible since they have always been in-charge of managing IT infrastructure, applications, and files.
To get rid of spreadsheet risks, you’ll have to get rid of spreadsheets altogether
One remedy is to have a risk management activity that involves both IT personnel and spreadsheet users. But wouldn’t you want to get rid of the complexity of having to distribute the responsibilities between the two parties instead of just one?
Learn more about Denizon’s server application solutions and how you can get rid of spreadsheet risk issues.
More Spreadsheet Blogs
Spreadsheet Risks in Banks
Top 10 Disadvantages of Spreadsheets
Disadvantages of Spreadsheets – obstacles to compliance in the Healthcare Industry
How Internal Auditors can win the War against Spreadsheet Fraud
Spreadsheet Reporting – No Room in your company in an age of Business Intelligence
Still looking for a Way to Consolidate Excel Spreadsheets?
Disadvantages of Spreadsheets
Spreadsheet woes – ill equipped for an Agile Business Environment
Spreadsheet Fraud
Spreadsheet Woes – Limited features for easy adoption of a control framework
Spreadsheet woes – Burden in SOX Compliance and other Regulations
Spreadsheet Risk Issues
Server Application Solutions – Don’t let Spreadsheets hold your Business back
Why Spreadsheets can send the pillars of Solvency II crashing down
?
amazon.co.uk
?
amazon.com
Contact Us
- (+353)(0)1-443-3807 – IRL
- (+44)(0)20-7193-9751 – UK