Technology has been evolving at a fast pace. Changes are also happening simultaneously within different industries. Making a great difference in the business world right now is the trend of mobile working.
Thanks to platforms and tools, working while on the go is now easier and more streamlined. The field service industry also benefits from these technological advances.
Mobile technicians can now give excellent performance and do their job efficiently with no hands-on management needed.
Keep in mind that field service management is no joke. So, to achieve a smooth business and mobile worker management, you’ll need to invest in good mobile service management software.
But First, what is Mobile Working?
Mobile working is a method of working that is not tied to a single physical location.
It isn’t just about checking your emails on your phone or ringing your colleagues via Bluetooth while driving your car to the next appointment. It’s so much more intricate than that.
Effective mobile working means you’re mobilising your workers. Field technicians should have everything they need to complete their day to day work. You’re giving them their entire office in the form of a mobile device.
Mobile working, via a handheld device, allows field technicians to do the following:
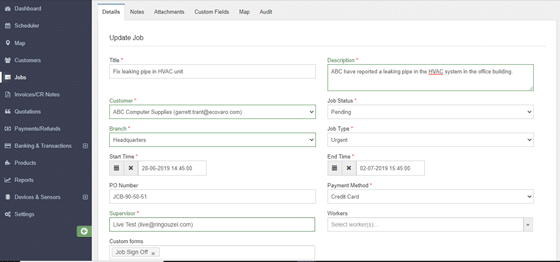
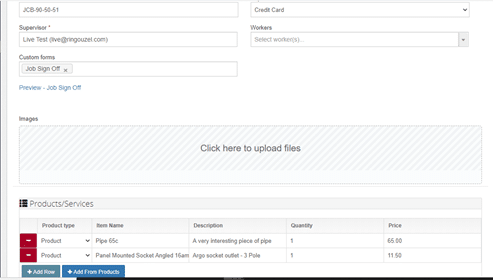
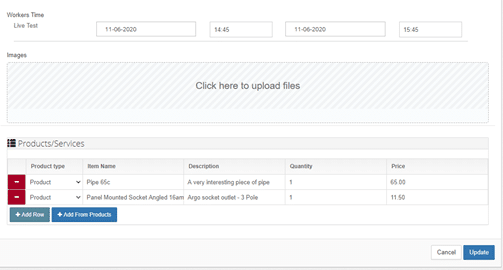
● Access and input information about a work order
● Collaborate on projects
● Stay in touch with colleagues, clients and management
● Utilize effectively the different software features
Your field workers should have the support of a dynamic management tool that ensures they are sent to the job that utilises their skills effectively and efficiently.
That’s where a good field service management software shows its importance.
The Role of a Field Service Management Software
Your mobile workforce is scattered across various physical locations. You’ll need to connect with them and simultaneously manage your field service business.
Thanks to the increasing connectivity and improvement of technologies for this purpose, mobile workers can easily input and access any work order details via your chosen field service management software.
What Makes a Good Field Service Management Software?
There are 3 main points to consider when investing in a good mobile workforce management software:
1. It’s simple and familiar to use. Like we mentioned before, be sure to mobilise your field technicians – not the back-office system. Make sure your chosen app or software has a simple user interface so your workers can be on-the-go easily.
2. It works offline. Rural areas and highways can have poor connectivity. Sometimes agents will need to work in areas that have little to no network coverage or are deep down working in tunnels or around heavy machines and turbines. You don’t want your field technicians unable to complete work due to connectivity issues. Make sure to choose software that can function on their device while offline.
3. It’s flexible (and maintainable). Your field service management of choice should have real-time visibility. Flexible and improved visibility for a field worker means that they can do their best in any task. They can share or get critical information about orders and customers. This drastically improves job completion rates and customer satisfaction.
Importance of Field Service Management Software to Mobile Working
Utilize the technology that is available to you. Your mobile workforce should have the right tools so they can make sure to do their fieldwork efficiently without worrying about tedious administrative work. Any back-office task can be done quickly through a field service management software.
And that’s the most important role of a great mobile service management app — effective mobile worker efficiency.
Benefits of a Field Service Management Software to Mobile Working
● Additional revenue: By simplifying the administrative work, your field technician can even double the work order in their daily shift, meaning more profit for the business.
● Cost-cutting: The cloud-based nature of a field service management software means that your business can reduce the cost of on-site IT.
Your mobile workforce can operate from wherever they have an online connection, meaning less reliance on offices and building costs.
● Boosts overall efficiency: A mobile workforce management software allows you as a manager to monitor in real-time where they are and what they are doing. It means that problems can be identified and dealt with immediately.
Your field technician, in turn, becomes more efficient because the technology allows them a quicker response, instead of taking too long finishing administrative tasks.
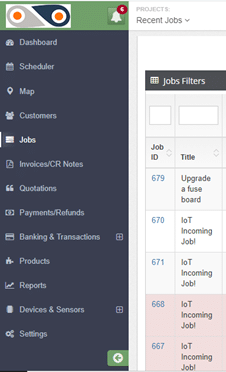
Invest in a great field service management software. Check out FieldElite and see how they can help you with the following mobile working features:
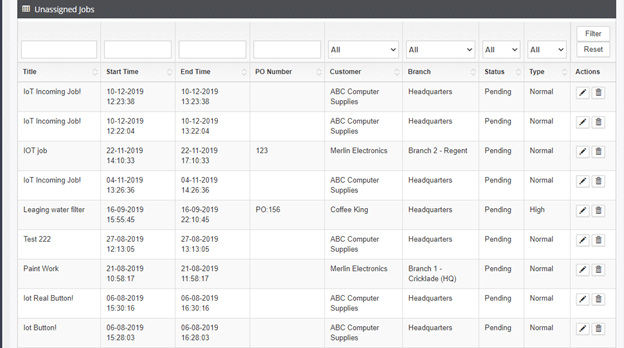
• Accepts jobs in the field
• Automate appointment scheduling
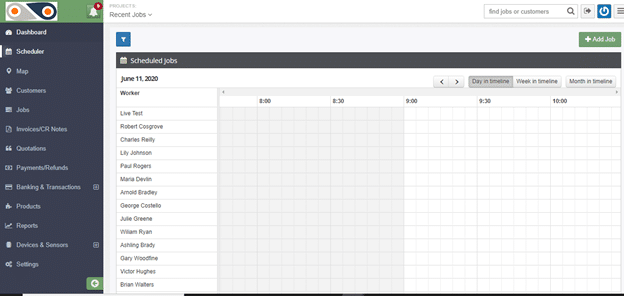
• Manage scheduled jobs
• Get real-time visibility into all operations
• Have a clear and easy viewing of job locations
• Resolve field service calls faster
• Enable mobile workers to get the job done right
• Keep customers updated at every step
• Create quotations and accept payments
• Analyse efficient reports from field technicians