The Japanese word Heijunka, pronounced hi-JUNE-kuh means ?levelling? in the sense of balancing workflows. It helps lean organizations shift priorities in the face of fluctuating customer demand. The goal is to have the entire operation working at the same pace throughout, by continuously adjusting the balance between predictability, flexibility, and stability to level out demand.
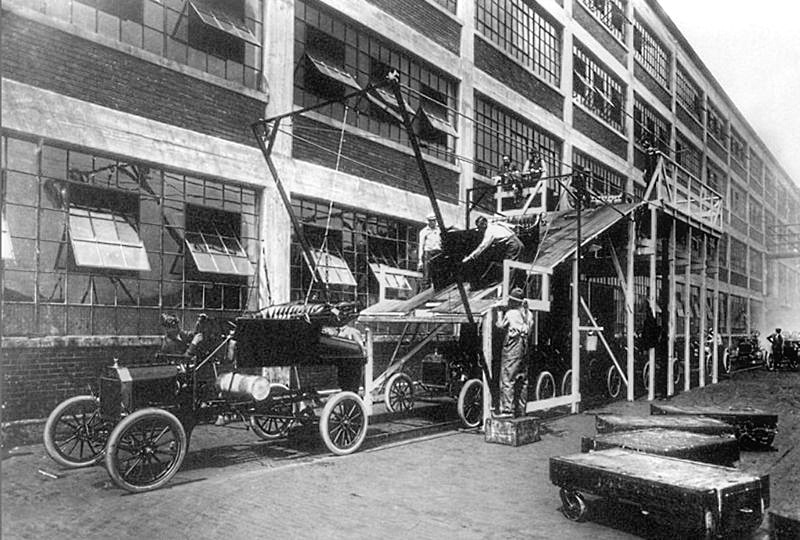
Henry Ford turned the American motor manufacturing industry upside down by mass-producing his iconic black motor cars on two separate production lines. In this photograph, body shells manufactured upstairs come down a ramp and drop onto a procession of cars almost ready to roll in 1913.
Smoothing Production in the Call Centre Industry
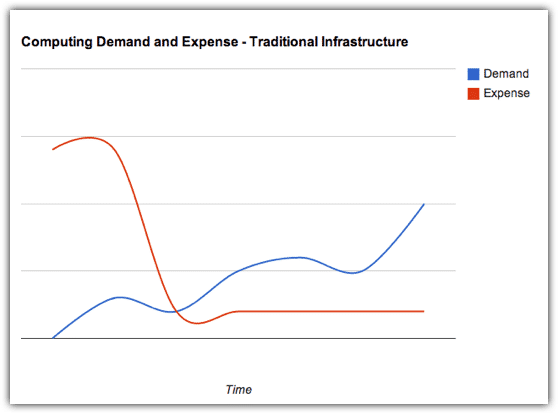
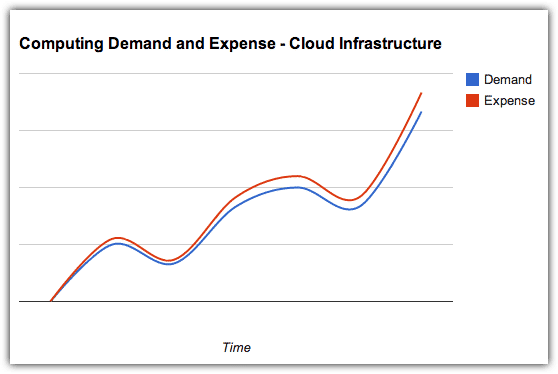
Call Centres work best in small teams, each with a supervisor to take over complex conversations. In the past, these tended to operate in silos with each group in semi-isolation representing a different set of clients. Calls came through to operators the instant the previous ones concluded. By the law of averages, inevitably one had more workload than the rest at a particular point in time as per this example.
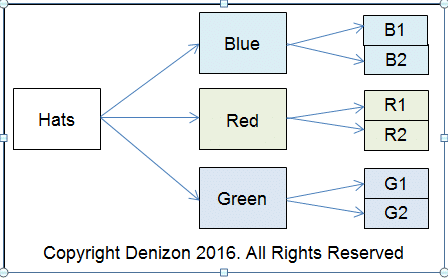
Modern telecoms technology makes it possible to switch incoming lines to different call centre teams, provided these are multi-skilled. A central operator controls this manually by observing imbalanced workflows on a visual system called a Heijunka Box. The following example comes from a different industry, and highlights how eight teams share uneven demand for six products.
This departure from building handmade automobiles allowed Henry to move his workforce around to eliminate bottlenecks. For example, if rolls of seat leather arrived late he could send extra hands upstairs to speed up the work there, while simultaneously slowing chassis production. Ford had the further advantage of a virtual monopoly in the affordable car market. He made his cars at the rate that suited him best, with waiting lists extending for months.
A Modern, More Flexible Approach
Forces of open competition and the Six Sigma drive for as-close-to-zero defects dictates a more flexible approach, as embodied in this image published by the Six Sigma organisation. This represents an ideal state. In reality, one force usually has greater influence, for example decreasing stability enforces a more flexible approach.
Years ago, Japanese car manufacturer Toyota moved away from batching in favour of a more customer-centric approach, whereby buyers could customise orders from options held in stock for different variations of the same basic model. The most effective approach lies somewhere between Henry Ford?s inflexibility and Toyota?s openness, subject to the circumstances at the moment.
A Worked Factory Example
The following diagram suggests a practical Heijunka application in a factory producing three colours of identical hats. There are two machines for each option, one or both of which may be running. In the event of a large order for say blue hats, the company has the option of shifting some blue raw material to the red and green lines so to have the entire operation working at a similar rate.
Predictability, Flexibility, and Stability at Call Centre Service
The rate of incoming calls is a moving average characterised by spikes in demand. Since the caller has no knowledge whether high activity advisories are genuine, it is important to service them as quickly as possible. Lean process engineering provides technology to facilitate flexibility. Depending on individual circumstances, each call centre may have its own definition of what constitutes an acceptably stable situation.
Contact Us
- (+353)(0)1-443-3807 – IRL
- (+44)(0)20-7193-9751 – UK